How to Protect Your Phone Number: 9 Simple Safety Rules
You start getting calls from unfamiliar numbers. Then more. Then the pattern becomes relentless, and you can't trace it to any single moment when things went wrong. That's usually how it works. According to Statista's 2024 data breach analysis, over 278.83 million individuals were affected by data compromises in the U.S. in 2024 alone, with phone numbers among the most commonly exposed personal identifiers in those records.
Your phone number is one of your most exposed data points, and most people don't treat it that way. It gets entered into forms, listed on profiles, shared casually in promotions, and stored across dozens of apps and services. Each of those touchpoints is a potential entry into a spam database or scam network. Phone number protection is not a one-time fix. It is a set of ongoing habits that reduce how widely your number circulates and how easy it is to target you.
Why Is It Important to Protect Your Phone Number?
Your phone number functions as an identity key. Services use it for account verification, two-factor authentication, billing, and account recovery. That means your number is not just a contact detail. It is a credential.
When your number is exposed, scammers and spam networks gain the ability to reach you directly, impersonate services you use, and attempt to extract money or account access through the kinds of [common phone scams] that rely on caller trust and manufactured urgency. The more places your number appears, the more likely it is to surface in a spam list, a phishing campaign, or a targeted fraud attempt.
How Do Phone Numbers Get Exposed in the First Place?
Through everyday actions: online signups, app permissions, public listings, and data collection practices that most users never see.
Every time you enter your number into a website or app, that data enters a pipeline. Some of it stays with the service you signed up for. Some of it gets shared with third-party marketing partners. Some end up with data brokers who build detailed profiles and sell them to anyone who pays. According to the Privacy Rights Clearinghouse, there are now over 750 registered data brokers in the U.S., all compiling personal data, including phone numbers, often without the knowledge of the people whose information they hold.
The most common everyday exposure points include:
- App sign-ups and account registrations that collect your number for verification and then share it with marketing partners
- Online promotions, contests, and giveaways designed to harvest contact data under the guise of prizes
- Social media profiles and public directory listings that make your number discoverable to automated scrapers
- Data breaches at companies holding your number, which release it to third-party spam and fraud networks
- Marketplace and classified listings, where you post your number for short-term purposes, but it remains indexed afterward
Automated scraping tools collect this information continuously, meaning exposure from even a briefly posted number can have lasting consequences.
What Are the 9 Simple Rules to Protect Your Phone Number?
Rule 1: Only Share Your Number When Absolutely Necessary
Before entering your phone number anywhere, ask whether the service genuinely requires it. Many forms include a phone number field by default, even when the service would work fine with just an email address. Subscriptions, newsletters, and content downloads rarely need a phone number. Treating your number as something to share only when truly necessary limits the number of pipelines it enters.
When a site or app insists on a phone number without a clear reason, that insistence is often a sign that the number is the actual product.
Rule 2: Avoid Posting Your Number Publicly
Any phone number posted on a public webpage can be scraped and added to a spam list within hours. This includes social media bios, forum profiles, marketplace listings, and comment sections. Even if you delete the original post, cached and archived versions may persist.
Audit your current public presence. Search your own phone number online periodically to see where it appears. If you find it on directories or people-search sites, most offer an opt-out process that removes or suppresses the listing.
Rule 3: Use Privacy Settings on Apps and Platforms
Many apps and platforms store your phone number in account settings for verification purposes, and some default to making that information more visible than it needs to be. Facebook, LinkedIn, and similar platforms all allow you to control who can see your contact details, but the defaults often favor visibility over privacy.
Check the privacy settings on every platform where you have an account and restrict contact information to the minimum necessary audience. On most platforms, your phone number should be visible to no one outside the platform itself.
Rule 4: Be Careful With Giveaways and Promotions
Contests, giveaways, discount code forms, and free trial offers frequently collect phone numbers as their primary purpose, with the product or prize being secondary. These campaigns often exist specifically to build marketing lists that get resold to advertisers, data brokers, and in some cases, spam networks.
A useful test: if the offer requires your phone number but there's no obvious reason why a winner notification couldn't be sent by email, the number is likely the real objective of the form. Skipping or using a secondary number for these situations reduces the risk considerably.
Rule 5: Don't Answer or Engage With Unknown Calls
Every time you answer a call from an unknown number, you confirm to the calling system that your number is active and monitored. That signal has value in spam and scam ecosystems: it increases the likelihood of follow-up targeting and can result in your number being flagged as a higher-value contact for resale.
Silent or one-ring calls follow the same logic. They are automated probes designed to detect active numbers. Letting unknown calls go to voicemail, and only returning calls to numbers you can verify, removes your number from the "confirmed active" category, which makes it more attractive to further targeting.
Rule 6: Use a Secondary Number When Possible
A secondary number, through a virtual phone service or a separate SIM, acts as a buffer between your primary number and the services and situations that carry a higher exposure risk. Use it for online purchases, promotions, app sign-ups, and any situation where you're uncertain how the number will be used.
If the secondary number ends up in spam databases, your primary number remains unaffected. This separation is one of the most effective structural changes you can make to protect phone number privacy long-term.
Rule 7: Regularly Review and Remove Old Accounts
Old accounts at services you no longer use may still hold your phone number in their database. If those services are later breached, your number is exposed without any recent action on your part. According to IBM's 2025 breach research via Secureframe, over 53% of all data breaches involve customer personal identifiable information, which routinely includes phone numbers.
Periodically audit your active accounts using these steps:
- List every service where you have an account and identify which ones you no longer actively use
- Delete or deactivate dormant accounts rather than simply stopping their use
- Request data deletion explicitly where the platform allows it, rather than assuming deactivation removes your data
- Check breach notification services like Have I Been Pwned to see if any of your accounts have already been compromised
This reduces the number of databases where your number exists as a live record and limits the blast radius of any future breach.
Rule 8: Block and Report Suspicious Numbers
Blocking a number after a spam or scam call prevents repeat contact from that specific line. Reporting does something more useful at scale: it contributes to detection systems that protect other users from the same number.
Forward suspected spam texts to 7726 (SPAM), which most major U.S. carriers support. File reports with the FTC at ReportFraud.ftc.gov for calls that appear to be active fraud attempts. These actions take under a minute and improve the accuracy of spam detection systems over time for everyone using them.
Rule 9: Use Caller ID and Spam Protection Tools
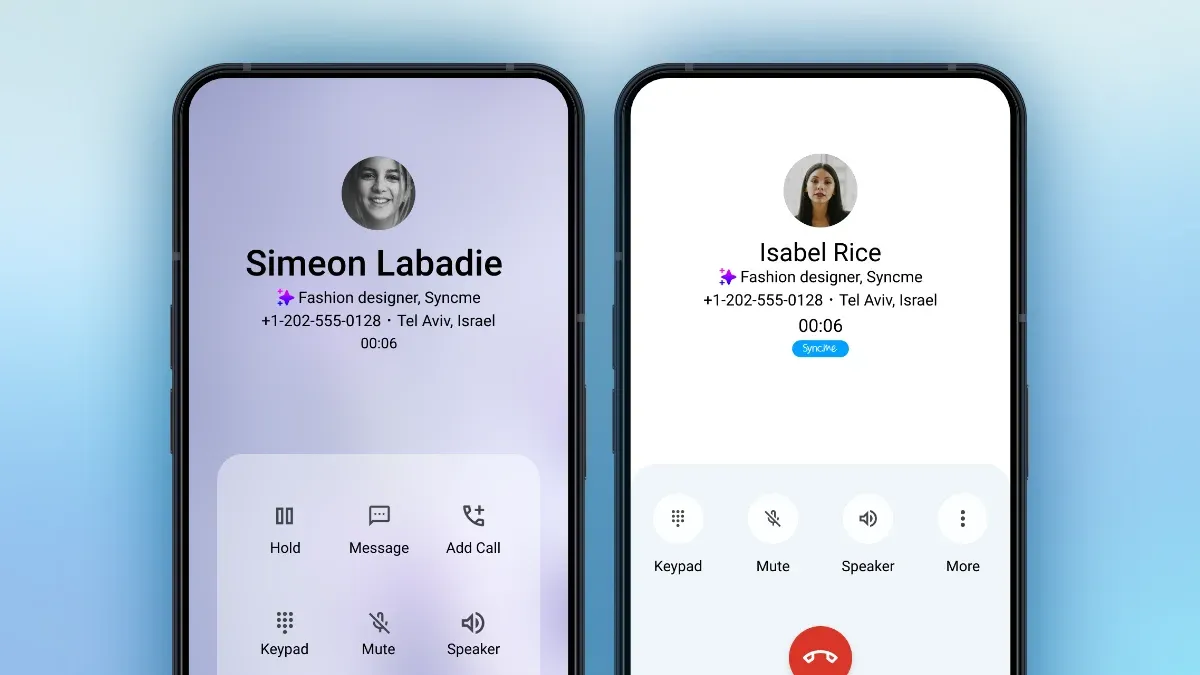
Real-time caller identification gives you the context to make an informed decision before you answer any unknown call. Instead of guessing, you see whether a number is flagged by other users, associated with a known spam operation, or genuinely unidentified.
Sync.me provides real-time caller ID using a database of over 5 billion phone numbers, combined with spam and fraud blocking and AI-powered insights on unknown callers. The spam protection features work across Android and iPhone, identifying calls that carrier systems alone may miss. This kind of real-time identification is one of the lowest-effort, highest-impact tools available for ongoing phone number protection.
What's the Best Way to Start Protecting Your Phone Number Today?
Start with one or two rules and build from there. Trying to overhaul everything at once is unlikely to stick.
The most accessible first steps you can take today:
- Search your phone number online to see where it currently appears and request removal from any directories you find
- Adjust privacy settings on your social media accounts so your number is visible to no one outside the platform
- Install a caller ID app that flags suspicious numbers before you pick up
- Delete two or three old accounts you no longer use and request data deletion
Those actions address the most common exposure points and the most common entry point for scam calls, without requiring significant time investment.
Protecting your phone number is not a one-time task. It is an ongoing practice. The landscape of data exposure changes constantly: new services, new breaches, new scam tactics. Staying consistent with these habits means you don't need to react to each new threat individually. The protection is already in place.
Take the first step right now
Download Sync.me free on Android or iPhone and add real-time spam detection and caller ID to every call you receive.
Frequently Asked Questions
Yes, in most jurisdictions, your phone number qualifies as personal data under privacy law because it can be used to identify you directly. In the U.S., it is treated as personally identifiable information (PII). In the EU, it is explicitly covered under GDPR. This means companies collecting it are subject to data handling obligations, though enforcement varies significantly.
Changing your number provides a temporary reset, but it only helps if you pair it with new habits around how you share and protect the replacement. If you continue using your new number the same way, it will accumulate in spam databases over time. Changing numbers makes most sense when you're experiencing an unusually high volume of targeted or harassing calls and want a clean start alongside better habits going forward.
Apps typically collect your phone number when you provide it during sign-up or verification. Some apps also request access to your phone's contacts or call logs through permission requests, which can expose associated numbers. Others purchase data from brokers or receive it through third-party integrations. Reviewing app permissions regularly and limiting what you share during sign-up reduces this exposure.
Completely removing your number from all online sources is difficult, but significantly reducing its visibility is achievable. You can request opt-outs from people-search sites and data brokers individually, though it requires repeated effort as data tends to reappear. Several paid data removal services automate this process. The Privacy Rights Clearinghouse data broker directory is a free starting point for identifying which brokers hold your information.
Share it only when genuinely necessary, with services that have clear privacy policies and opt-out options. For situations with uncertain privacy practices, such as promotions, marketplace listings, or new apps, use a secondary or virtual number rather than your primary one. Avoid posting your number in any publicly accessible format, and never enter it into forms that don't clearly explain why they need it.
مقالات ذات صلة
How to Find the Owner of a Phone Number: 7 Proven Methods
Learn how to find the owner of a phone number using 7 proven, legal methods. Compare free and paid lookup tools to identify unknown callers safely.
Top 10 Ways to Check Online Phone Number
Learn effective ways to check online phone number sources and identify unknown callers. Protect yourself from scams and verify business contacts.